

The annual Rising in Cyber List showcases the most promising private cybersecurity companies, as selected by 150 leading CISOs and operating security executives across the industry. The startups have been segmented into three buckets (data as of Q1 2026):
Early ($1M-$35M raised), Mid ($35M-$100M raised), Late ($100M+ raised)


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

Redefining identity security for how people and AI agents work today.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

Build your security operations your way with composable SIEM.
%2520-%2520Shimon%2520Freedman%25201.png)

Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.
%2520-%2520Shimon%2520Freedman%25201.png)
Anecdotes is the leading Agentic GRC platform built for the enterprise.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

The security data and agent platform built for defenders who build.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

One platform to secure AI — from data to access to real-time protection.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

The trust network that enables businesses to operate, scale, and partner with confidence.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

Redefining cloud-native infrastructure with vulnerability-free software artifacts – from container base images to libraries, VMs, helm charts, EOL support, and more.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

The agentic application security platform that understands your code and business logic, delivering zero distractions for developers.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

Enables identity-driven governance for SaaS and AI environments.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

We give you the control to unlock safe, fast AI adoption.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.
%2520-%2520Gadi%2520Evron%25201.png)

Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

Discovers, governs, and protects AI and Agents across the enterprise, from homegrown AI to SaaS agents and coding assistants.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

Runtime security that sees, detects, and stops modern attacks.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

Thrive securely in the cloud, from observation to action.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

The most advanced platform for security teams.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

One platform for enterprises to run MCPs, Skills, and Agents securely.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

Ship fast while Socket protects your open source supply chain from vulnerable and malicious code.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

On a mission to power the world's most important workflows.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

Transforming cybersecurity with the Torq AI SOC Platform that empowers enterprises to instantly and precisely detect and respond to security events at scale.
By Dave Chen, Co-Head of Global Technology Investment Banking, Morgan Stanley and Oren Yunger, Managing Partner, Notable Capital
For CISOs, the early AI results are energizing: Capabilities like AI-powered penetration testing and threat detection are helping augment existing cybersecurity, overcome talent gaps, and respond to issues with more authority. But across enterprises, AI adoption is also outpacing security. Now, CISOs are quickly shifting their focus to safeguarding these new workloads, a pivot poised to shake up legacy cybersecurity markets.
Overall, the security market is bustling and expected to grow to $255 billion by 2029, based on IDC estimates. Startups are innovating, growing, and attracting investor attention at unparalleled speed and scale, while the leading AI labs are rapidly layering security capabilities over their powerful LLMs. And despite the panic in the public markets, many incumbent security software vendors appear increasingly well-positioned to survive the near-term impact — especially as they continue to pay a premium for capabilities that keep them competitive.
But when AI advancements impacting the cybersecurity sector can shed billions of dollars from the market, and landscape-shifting technical advancements are a regular occurrence, CISOs are left grappling with key questions: Should we invest in an AI-native solution, double down on existing platforms, or simply wait for the next LLM release and build our own?
The pressure is on CISOs to balance enablement and progress with safety. According to our recent survey of over nearly 150 security leaders from the world’s largest and most prominent businesses, 71% say their companies already have AI agents in production, only 11% report that they have mature, well-integrated, or best-in-class tooling to secure AI workloads. This is a dangerous gap. Luckily for CISOs, innovation in cybersecurity is in full swing.
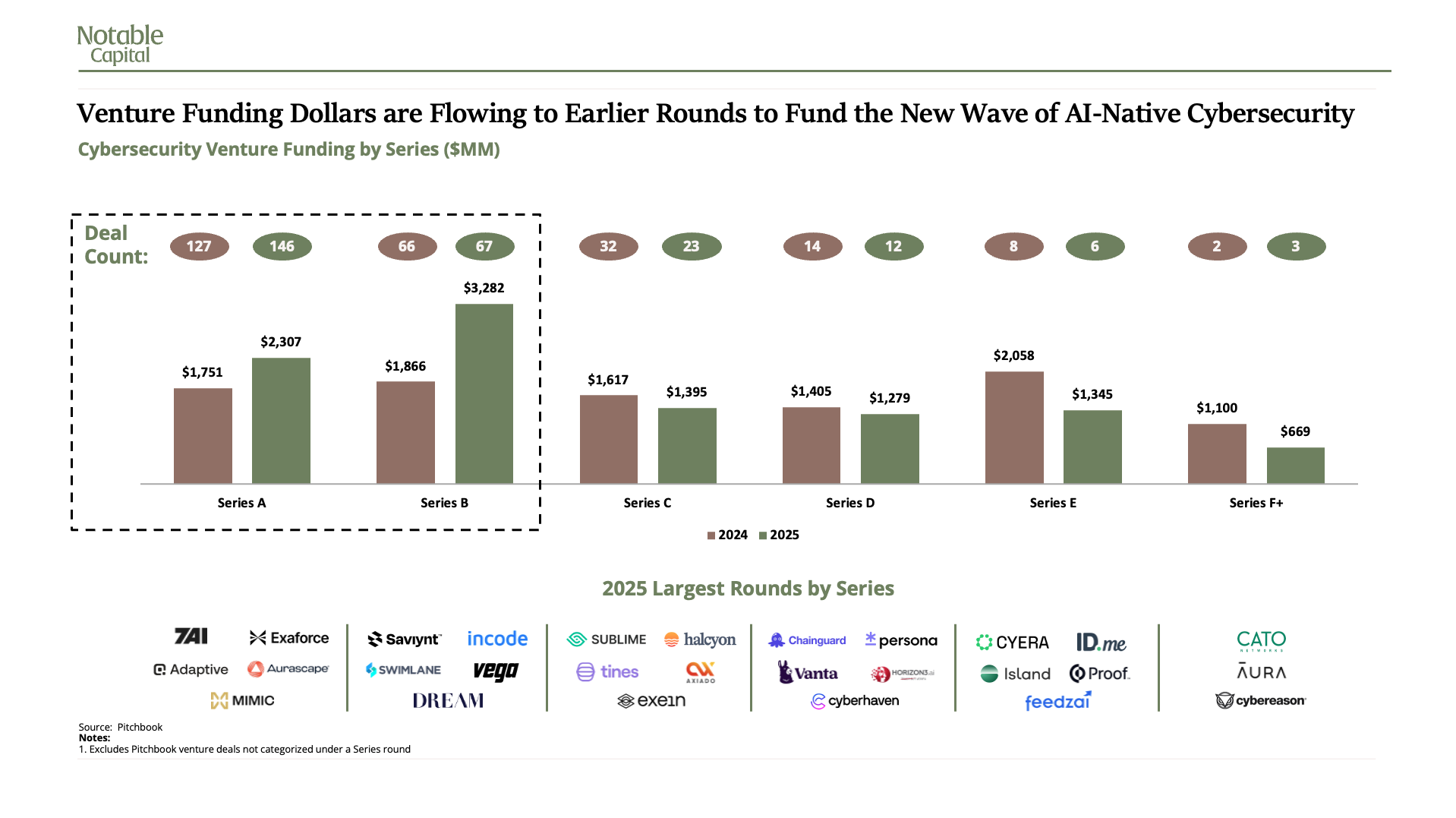
In 2025, Series A and B funding accounted for over half of the over $10 billion invested in cybersecurity startups. But with CISOs also taking a closer look at all their spending, it’s incumbent on younger companies tackling the challenge of AI security to quickly prove their real-world value. Otherwise, what is a diverse market could consolidate to existing platforms and frontier AI labs that move faster to earn customer trust.
Our 2026 Rising in Cyber Report, the second year running the study, examines survey insights from leading CISOs and market data from Morgan Stanley to make sense of how CISOs are navigating a period defined by rising uncertainty, expanding attack surfaces, and rapid shifts in both risk and opportunity.
In the AI era, the top cybersecurity challenges may seem familiar: eliminating blind spots, securing identities, managing access, and responding to deviations. But as AI agents swarm technology environments, these long-standing problems are becoming existential threats.
CISOs are trying to keep up: over 50% are already using AI agents in their own security operations, according to our survey. And budgets are growing to do even more.
“AI is really helping us work smarter and faster on challenges that have historically been difficult to scale, like triaging and prioritizing security issues. It becomes more manageable when you can augment your team with that kind of capability," said United Airlines’ Vice President and CISO Deneen DeFiore.
Meanwhile, investors are flocking to young, AI-native startups that can help secure new AI technology. And major platforms continue to scoop up specialized vendors that help them keep pace with innovation in the market, like Cisco’s acquisition of Astrix.
The Rising in Cyber 2026 Report delivers a snapshot of the current state of play of the cybersecurity industry. Based on survey insights from leading CISOs and market data from Morgan Stanley, it spotlights the ways AI is changing how CISOs think about their core technology and separates hype from reality to help investors, operators, security leaders, and founders make sense of the chaos.
There’s no shortage of demand. Overall, the cybersecurity market is expected to grow to $255 billion by 2029, according to IDC data, up from a higher-than-expected $153 billion in 2025. Powering this growth are expected double-digit increases in enterprise spend on identity and access management (IAM), data and information security, and cloud-native application protection solutions, among other segments. The market also remains highly fragmented. Few vendors command more than 20% of any vertical. But Microsoft is the dominant force in five of the largest verticals.


In 2024, private equity firms paid up for security startups: Thoma Bravo bought Darktrace ($5.5 billion) and EQT bought Avetta ($3 billion), according to PitchBook data.
Last year marked a clear shift toward platform-led consolidation. Beyond the $32 billion Wiz deal, Palo Alto spent nearly $30 billion to acquire both CyberArk and Chronosphere, and ServiceNow bought Armis for $7.8 billion. And the number of acquirers is growing more diverse as companies like Veeam get more aggressive about security on their platforms.
Overall, strategic M&A deal volume grew to $81 billion, up over 4x from 2024, while buyouts shrank to just $6 billion. Even without the blockbuster Wiz deal, overall M&A activity increased 156%.
The momentum isn’t slowing down, either, as AI pushes the large incumbents to evolve their platforms. So far in 2026, CrowdStrike purchased SGNL, Palo Alto Networks purchased Koi, and Sophos acquired Arco Cyber, among other deals.


While public cybersecurity stocks weren't immune to investor whiplash, the sector performed better on average than its infrastructure and application software counterparts, indicating the resilience of security tools amid the broader IT overhaul. Overall, security software shares were up 1%, compared to a 5% decline in infrastructure software and a 21% decline in application software. Perhaps unsurprising: the biggest sell-offs were tied to market concerns about the impact of AI.
Early-stage, AI-native startups dominated the VC funding landscape. Together, investment in Series A and B startups eclipsed $5.5 billion in 2025 — the only segment that didn’t decline year-over-year.
Investments are coming earlier, getting bigger, and happening faster. For example, in total, Series B rounds grew 74% to $3.3 billion, while deal count went from just 66 to 67. Annual deal size also went up 75% to $49 million. And increasingly investor attention is on technology that will help companies secure their new AI use cases: 7AI, Adaptive, and Exaforce, which all closed early-stage funding rounds.
While financiers rush to back AI infrastructure and coding startups registering triple-digit growth, cybersecurity is a much different market. It’s clear investors are prioritizing innovation, and are comfortable with the industry’s slower pace of growth and change. And between a frothy funding landscape and hyperactive M&A market, the liquidity and exit opportunities for startups are ample.
What is your organization's current stance on deploying AI agents in production environments?
How would you rate your current tooling for securing AI workloads (including agents, MCP, etc.)?
Cybersecurity teams are eager to adopt AI — and increasingly have the budget to do so. Many have already embraced AI in their own work. But as AI makes long-standing challenges like identity and access management more troublesome, the question is how quickly teams can onboard the capabilities needed to keep environments protected.
To understand how AI is shifting priorities, budgets, and operations, we surveyed nearly 150 CISOs and security leaders. The biggest findings include:
AI and cybersecurity are increasingly intertwined, and the benefits are coming into focus: Today, AI agents are helping teams overcome talent shortages, detect issues in applications, and do more with less. For example, for many companies, penetration testing used to be a bi-annual event. Now, AI agents can work continuously in the background, alerting teams to concerns in near real-time. But for some CISOs, the challenge is now turning the abundance of new intelligence into real-world results: "Across the industry, organizations are solving individual problems with great tools, and that gives us real visibility. The next frontier is turning that visibility into coordinated action," said United Airlines’ Vice President and CISO Deneen DeFiore.
Where do you feel AI has contributed to provide better security, privacy, and compliance for your organization?
The opportunity for AI startups is securing rapidly growing AI use cases: Over the next 12 months, rapid AI adoption will make evergreen problems worse. According to the survey, 21% of CISOs labeled identity and access management the most concerning AI-based threat, while 14% highlighted observability: "The market has not figured those two domains out,” said Delta Dental Plans Association CISO Alex Green. “In a perfect world, AI should be able to observe how agentic identities operate and infer what data they actually need to access and under which circumstances. That would solve the vast majority of our problems as agents proliferate,” he added.
Which of the following AI-based threats are you most concerned about in the next 12 months?
CISOs have more money to spend, but more demands on their budgets: A quarter of security leaders expect budgets to increase as much as 10%, while nearly one-third expect gains of as much as 30%. But while coffers may be growing, so are the demands on those funds. More money doesn’t necessarily mean more talent or vendors. Increasingly, CISOs are also looking at how they can build agentic capabilities to enhance their preventative, detective, and response capabilities, while also reducing costs.
Please indicate how your cybersecurity budget has changed between 2025 and 2026
What percentage of your security budget is currently allocated to supporting AI enablement within your organization?
AI is adding new wrinkles to the classic “build vs. buy” debate, and many CISOs are still figuring out the new balance.
AI coding tools make it easier than ever for internal teams to build applications or extend existing platform capabilities. Security leaders are embracing the opportunity to consolidate a vendor-heavy landscape with custom-built tools and flexible systems that their employees can easily integrate.
“Teams, especially engineering-driven ones, will innovate with the latest AI products and tools faster than ever before,” said Jiphun Satapathy, CISO at Motive.
While CISOs may be able to sunset some external point solutions, replacing the foundational, battle-tested platforms will be much tougher — especially as AI makes it easier for these large providers to innovate at the speed of smaller rivals.
“Building or adding new capabilities will be much less expensive and much faster than it used to be,” said Jiphun Satapathy. As a result, “platforms are expanding much quicker than they have in the past,” he added.
For example, web application firewalls used to be one of the largest portions of Delta Dental’s security budget. Now, with WAF a largely commoditized capability and available within most security platforms, the team can monitor and block suspicious or malicious network traffic for much cheaper. As a result, investment was redirected to data security, a growing problem as AI expands access.
“Because AI has helped us be more effective with legacy problems, we’ve been able to find the money for newer problems,” said Delta Dental’s Alex Green. “Now, data security is the largest line item in the budget.”
Security teams have a reputation as early technology adopters. But cutting-edge capabilities are now replicated by competitors in months, not years — either by platform providers, other startups, or the AI labs. In the time it takes to implement and integrate a new tool, a more appropriate one may have already come along.
It’s why CISOs are more willing to wait longer to invest in best-of-breed solutions: “When there’s a great, niche AI security capability, a month later it’s now in six other tools that also have way more functionality,” said Green.
But despite tougher competition from platform providers and more stringent evaluations from potential customers, specialized, standalone applications will still be vital to security operations, especially to keep CISOs from consolidating too much to a single provider.
“We don't want to get tightly tied to a vendor product. Lock-in is a real issue,” said Motive’s Jiphun Satapathy.
Whenever there are technology transformations of this magnitude, adoption always outpaces security. But AI is much different than past revolutions, and the consequences of poor security are far more significant. Now, even minor issues can quickly become crises that tarnish brand reputations and impact growth.
There’s an urgent need for more powerful security tooling, but CISOs have more flexibility than ever before in how they onboard the capabilities they need. The smartest CISOs will use a combination of building, buying, and extending existing platforms to improve how their own teams function, and protect the business as the AI generation progresses.
Our Rising in Cyber 2026 list is evidence of how quickly AI-native startups are challenging legacy markets. While CISOs may be one step behind AI adoption today, the technology is here to help them get back to a confident security stance.
Thank you to Al Ghous, Laura Hamilton, Emily Stanford, Laura Gravley, Shilpi Saran, Calvin Patel, and Kyler Miyashita for their contributions to the report.












We have prepared the information contained on this website solely for informational purposes. You should not definitively rely upon it or use it to form the definitive basis for any decision, contract, commitment or action whatsoever, with respect to anyproposed transaction or otherwise.
We have prepared the information contained on this website based, in part, on certain assumptions and information obtained by us from various sources. Our use of such assumptions and information does not imply that we have independently verified or necessarily agree with any of such assumptions or information, and we have assumed and relied upon the accuracy and completeness of such assumptions and information for purposes of preparing the information contained on this website. Neither we nor any of our affiliates, or our or their respective officers, employees or agents, make any representation or warranty, express or implied, in relation to the accuracy or completeness of the information contained on this website or any oral information provided in connection herewith, or any data it generates and accept no responsibility, obligation or liability (whether direct or indirect, in contract, tort or otherwise) in relation to any of such information. We and our affiliates and our and their respective officers, employees and agents expressly disclaim any and all liability which may be based on the information on this website and any errors therein or omissions therefrom. Neither we nor any of our affiliates, or our or their respective officers, employees or agents, make any representation or warranty, express or implied, that any transaction has been or may be effected on the terms or in the manner stated in on this website, or as to the achievement or reasonableness of future projections, management targets, estimates, prospects or returns, if any. Any views or terms contained on this website are preliminary only, and are based on financial, economic, market and other conditions prevailing as of the applicable date(s) such information is presented and/or as of the date such information is first presented and are therefore subject to change. We undertake no obligation or responsibility to update any of the information contained on this website. Past performance does not guarantee or predict future performance.
This website and the information contained on this website do not constitute legal, regulatory, accounting or tax advice. We recommend that you seek independent third party legal, regulatory, accounting and tax advice regarding the information contained on this website.
This website and the information contained on this website do not constitute and should not be considered as any form of financial opinion or recommendation by us or any of our affiliates. This website is not a research report.This website and the information contained on this website is provided by Notable Capital Management, L.L.C. and/or certain of its affiliates or other applicable entities in collaboration with other third parties.